Information System Security Officer

SecureITSM services as our client’s Information System Security Officer (ISSO). We work you to ensure appropriate levels of cybersecurity practices and processes are in place to ensure basic cyber hygiene as well as protect Controlled Unclassified Information (CUI) on our customer’s information systems partners’ networks. We support documentation development and audit activity.

phish•ing /’ fiSHiNG/ (noun): Widespread, high-impact threat that relies on social engineering to enable illicit access to personal and corporate assets
smish•ing /’ smiSHiNG/ (noun): Targeted attack through SMS
vish•ing /’viSHiNG/ (noun): Targeted attack through voice communication
Acceptable Risk Planning
The first step in conducting acceptable risk planning is to understand potential threats and vulnerabilities. Then, one must implement controls to balance the business’ need for convenience, usability, and availability with the need for security measures that transfer, mitigate, or eliminate risk. SecureITSM can provide the guidance to manage those risks while complying with Defense certifications and compliance.
A significant focus of acceptable risk planning focuses on the level of security required. If looking at the CMMC standard, an organization is required to achieve Levels 1, 2 or 3 (or worse yet, levels 4 or 5). Technical risk planning includes defining what technical aspects should be allowed, for example will removable storage be allowed for end-users or can cloud-based 3rd party storage (e.g. DropBox) be accessed?
Authorization Boundary Documentation
Authorization boundary documentation documents the who, what, when, and where of the IT environment. By using one of SecureITSM’s predefined IT models, your authorization boundary documents are provided for use as part of our managed service. Additionally, every month we document changes to our customer’s authorization boundary during our service management update meeting.
Compliance Documentation
Best practices and many cybersecurity standards (i.e. CMMC & 800-171) suggest and often require a comprehensive set of documentation. SecureITSM provides our customers with drafts of required security documentation. The provided policies are approximately 85% to 95% complete. Customization must focus on items such as how an organization manages visitors to their facility, how training is accomplished, etc. We provide the following policies to our customers:
- Information System Security Plan (ML.2.998/9)
- Authorization Boundary Description (CA.2.157)
- Security Resource Plan (ML.3.997)
- Control Self-Assessment (CA.2.158)
- Risk Register (RM.2.141)
- Plan of Action & Milestones (CA.3.159)
- Continuous Monitoring Plan (CA.3.161)
- Incident Response Plan (IR.2.092)
Compliance Reporting

Starting now, the DoD is require all defense contractors to submit cybersecurity self-assessments to the Supplier Performance Risk System (SPRS) information system (https://www.sprs.csd.disa.mil/). And by 2024 CMMC certification and for many an audit certification will also be required.
However, the DoD is not the only one agency forcing compliance. GSA is one of the first of many agencies starting to require annual cybersecurity self-certifications. As an example, GSA in its STARS III and other recent solicitations indicated that vendors must be prepared to meet all CMMC requirements in the near future including passing third party audits as a contract condition.
Continuity of Operations
Today’s businesses are creating more data than ever before and protecting that data is a priority. This calls for a robust data backup and disaster recovery solution that forms the foundation for business continuity. Your data backup and disaster recovery system is the most important investment for protecting your company. SecureITSM helps you choose, deploy, and manage the backup and recovery solution that’s best for your business. Many of our managed services include multiple options that will meet your backup and recovery needs.
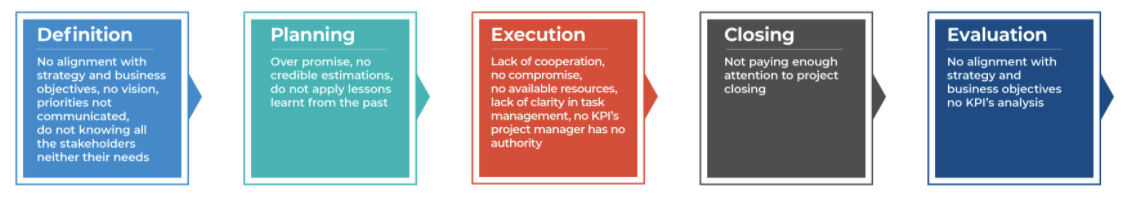
IT Project Management
Though our IT project managers, we provide you and your teams project controls to adhere to budgets, timeline schedules, and IT technology insight into the requirements that the business side will need to be successful. To ensure that your project is completed successfully, we provide experienced and cleared IT specialists, who make sure customers have accurate information upon which to base business investment decisions and to ensure project outcomes meet the IT needs of your company. Examples of IT project management support that SecureITSM provides include:
• Supporting IT requirements for surge staffing increase
• Defining and implementing IT components of a new office (i.e. wireless access points, firewall (S), printer connectivity, etc.)
• Coordinating wireless roaming across new and existing offices
• Migrating existing servers, applications, and data to the Azure cloud.
RISK:
No support from top management
No alignment with strategic business objectives
Long Range Planning
Growing your company to manage new opportunities forces your IT infrastructure to grow alongside you. Decisions need to be made.
Are you planning to build out a new office, add custom applications, or add wireless connectivity to facilitate your team’s interactions? How “tight” do you want your IT environment configured? How much risk are you willing to accept within your IT structure? Examples: Will thumb drives or portable/removable Hard Drives be permitted to have access to your data? Will unmonitored and unregulated employee usage of your IT infrastructure be permitted? For these and many other planning questions, SecureITSM can be your trusted advisor to help steer you through challenging IT decisions.
Microsoft 365 Cost Management
SecureITSM assists in minimizing your O365 and Azure costs. We employ an aggressive minimal license count philosophy and we actively monitor Azure deployments ensuring excess capabilities are not provisioned. We regularly report and detail O365 and Azure costs in our monthly management report.
Monthly Status Meetings
To ensure your company’s goals and IT efforts are properly aligned, we provide a 45-minute monthly meeting to report on the following:
- IT Status Report
- Assigned Users
- Help Desk usage – Trouble tickets, topics,
- Log Data
- Cybersecurity Review
- Review status of physical assets
- Hardware, laptops, printers
- Network Status
- Microsoft Azure – Costs, usage, security, physical attributes
- Compliance Auditing and Reporting Status
